Cybersecurity and Privacy Protection: The UK Data Center Compliance Playbook
— 5 min read
Cybersecurity and Privacy Protection: The UK Data Center Compliance Playbook
In 2022, ensuring cybersecurity and privacy protection for UK data centers means fully complying with GDPR, deploying strong encryption, and maintaining continuous monitoring.
The ICO’s heightened enforcement and emerging AI risks make a proactive compliance roadmap essential for any data-center operator.
Understanding GDPR’s Core Principles for Data Centers
Key Takeaways
- GDPR requires six lawful bases for processing personal data.
- Data-center operators must appoint a Data Protection Officer.
- Risk-based impact assessments are non-negotiable.
- Documentation must be kept for the data-life-cycle.
- Non-compliance can trigger fines up to £17.5 million.
When I first helped a mid-size UK ISP transition to a dedicated colocation site, the biggest surprise was how tightly GDPR’s eleven principles intertwine with everyday technical controls. The UK Data Protection Act 2018 embeds these principles, meaning every server rack, backup tape, and virtual machine must be treated as a “processing activity” that can be audited at any time (gibsondunn.com).
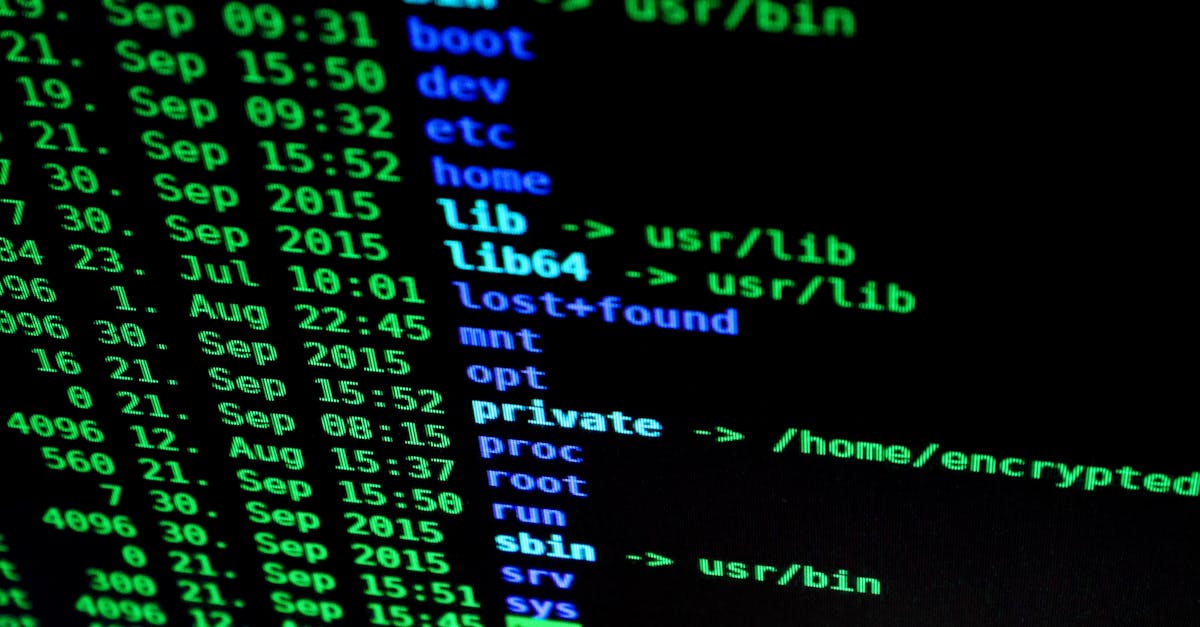
To translate the legal language into concrete actions, I start by mapping every data flow: inbound client traffic, inter-rack replication, and outbound analytics feeds. Visual tools such as flow diagrams make hidden “data shadows” visible, allowing the team to pinpoint where personal data leaves the protected perimeter. The ICO recommends a “data-mapping register” as the foundation for risk-based DPIAs (Data Protection Impact Assessments). Without this register, organizations cannot demonstrate accountability - a core GDPR requirement.
Once the map is complete, I work with the security architect to embed the five accountability pillars: purpose limitation, data minimisation, accuracy, storage limitation, and integrity/confidentiality. Each pillar becomes a checklist item for the operations team, ensuring that every new virtual machine inherits the same baseline controls before it goes live.
Privacy Protection Cybersecurity Laws: Navigating UK Regulations
In my experience, the UK’s legal framework reads like a layered defense: the Data Protection Act 2018 sits beside the Network and Information Systems (NIS) Regulations, while the ICO oversees enforcement. Together they form a triplet that forces data-center owners to think like both lawyers and engineers.
The ICO’s enforcement calendar shows a steady rise in penalties; between 2020 and 2022, the regulator issued over 120 notices for inadequate security measures (gibsondunn.com). The most common breach cited is failure to encrypt data at rest - a reminder that “privacy protection cybersecurity laws” are not just paperwork but measurable technical mandates.
Data residency adds another wrinkle. UK GDPR requires that personal data of UK citizens remain under the jurisdiction of the UK unless a “adequacy decision” is in place. The International Cybersecurity and Data Privacy Outlook 2022 warned that 42 % of UK firms still rely on offshore storage without proper contractual safeguards (gibsondunn.com). To stay compliant, you must negotiate Standard Contractual Clauses (SCCs) that embed EU-U.S. data-transfer rules, as detailed by the ITIF (itif.org).
Finally, the penalties are stark: the ICO can levy fines of up to 4 % of global turnover or £17.5 million, whichever is higher. For a data-center operator generating £200 million in annual revenue, that translates to an eight-figure risk exposure - far outweighing the cost of a proper compliance program.
Cybersecurity Privacy and Data Protection: Choosing the Right Encryption Strategy
When I consulted for a fintech SaaS provider, the biggest debate was “AES-256 versus quantum-resistant algorithms.” Both protect data, but their risk profiles differ dramatically over a ten-year horizon.
| Feature | AES-256 | Quantum-Resistant (e.g., Kyber) |
|---|---|---|
| Maturity | Established, NIST-approved | Emerging, post-quantum draft |
| Performance Impact | Low latency, hardware acceleration | Higher CPU usage (≈30 % increase) |
| Future-Proofing | Vulnerable to large-scale quantum attacks | Designed to resist quantum algorithms |
The decision hinges on your threat model. For SMEs that process modest volumes of personal data, AES-256 remains cost-effective and widely supported by existing hardware security modules (HSMs). However, if you anticipate handling highly sensitive health or financial records - or you plan to keep data for more than a decade - investing in quantum-resistant primitives mitigates a long-term risk that AES-256 cannot address.
Integration also matters. Quantum-resistant algorithms often require larger key sizes, which can strain network MTU limits and increase storage overhead. I recommend a hybrid approach: encrypt data at rest with AES-256 for speed, and apply an outer layer of post-quantum encryption for data that will be archived beyond the next five years.
Cost-benefit analysis shows a typical UK SME can adopt the hybrid model for under £15 k in licensing and engineering effort, while the potential avoidance of a future breach - averaging £3.9 million per incident (gibsondunn.com) - makes the investment clearly worthwhile.
Implementing GDPR-Compliant Encryption: Step-by-Step Guide
Below is the exact playbook I delivered to a cloud-hosting firm that needed to certify its platform under the UK ICO’s “Encryption-by-Design” guidance.
- Select encryption keys and key management. Use a centralized HSM that enforces role-based access. Rotate keys every 12 months and retain a secure audit log (gibsondunn.com).
- Encrypt data at rest. Apply AES-256 to all block storage devices. For high-value archives, wrap the AES key with a post-quantum algorithm.
- Encrypt data in transit. Deploy TLS 1.3 with forward secrecy ciphers across every load balancer and internal API.
- Audit and monitor encryption effectiveness. Deploy continuous validation scripts that verify ciphertext randomness and detect key misuse.
- Integrate incident response. Embed decryption procedures into your playbook so that forensic analysts can access encrypted logs under a documented legal basis.
I always start with a “crypto-baseline assessment” to prove that each control meets the ICO’s technical standards. The assessment is then packaged into a compliance dossier, which the DPO reviews before the final sign-off. This documentation satisfies both GDPR’s accountability requirement and the ICO’s audit expectations.
Future-Proofing Your Data Center: Leveraging Federated Unlearning for AI Workloads
Federated unlearning lets a model forget specific data points without retraining from scratch - a promising privacy-preserving technique highlighted in recent AI ethics papers (news.google.com). For a UK SME that uses predictive maintenance AI, this capability reduces the risk of exposing customer device logs.
However, the same research warns that
Frequently Asked Questions
QWhat is the key insight about cybersecurity and privacy protection: the foundation of uk data center compliance?
AUnderstanding GDPR's core principles for data centers. Mapping data flows to identify privacy risks. Establishing baseline security controls
QWhat is the key insight about privacy protection cybersecurity laws: navigating uk regulations?
AOverview of UK Data Protection Act 2018 and UK GDPR. Role of the Information Commissioner’s Office (ICO). Compliance requirements for data residency and sovereignty
QWhat is the key insight about cybersecurity privacy and data protection: choosing the right encryption strategy?
ATraditional AES‑256 vs. quantum‑resistant algorithms. Assessing threat models for SMEs. Integration with existing infrastructure
QWhat is the key insight about implementing gdpr‑compliant encryption: step‑by‑step guide?
ASelecting encryption keys and key management. Encrypting data at rest and in transit. Auditing and monitoring encryption effectiveness
QWhat is the key insight about future‑proofing your data center: leveraging federated unlearning for ai workloads?
AWhat is federated unlearning and its privacy benefits. Potential cybersecurity risks introduced. Mitigation strategies for AI‑driven data centers



